Incident Response Frameworks: Checklist for HDOs
Post Summary
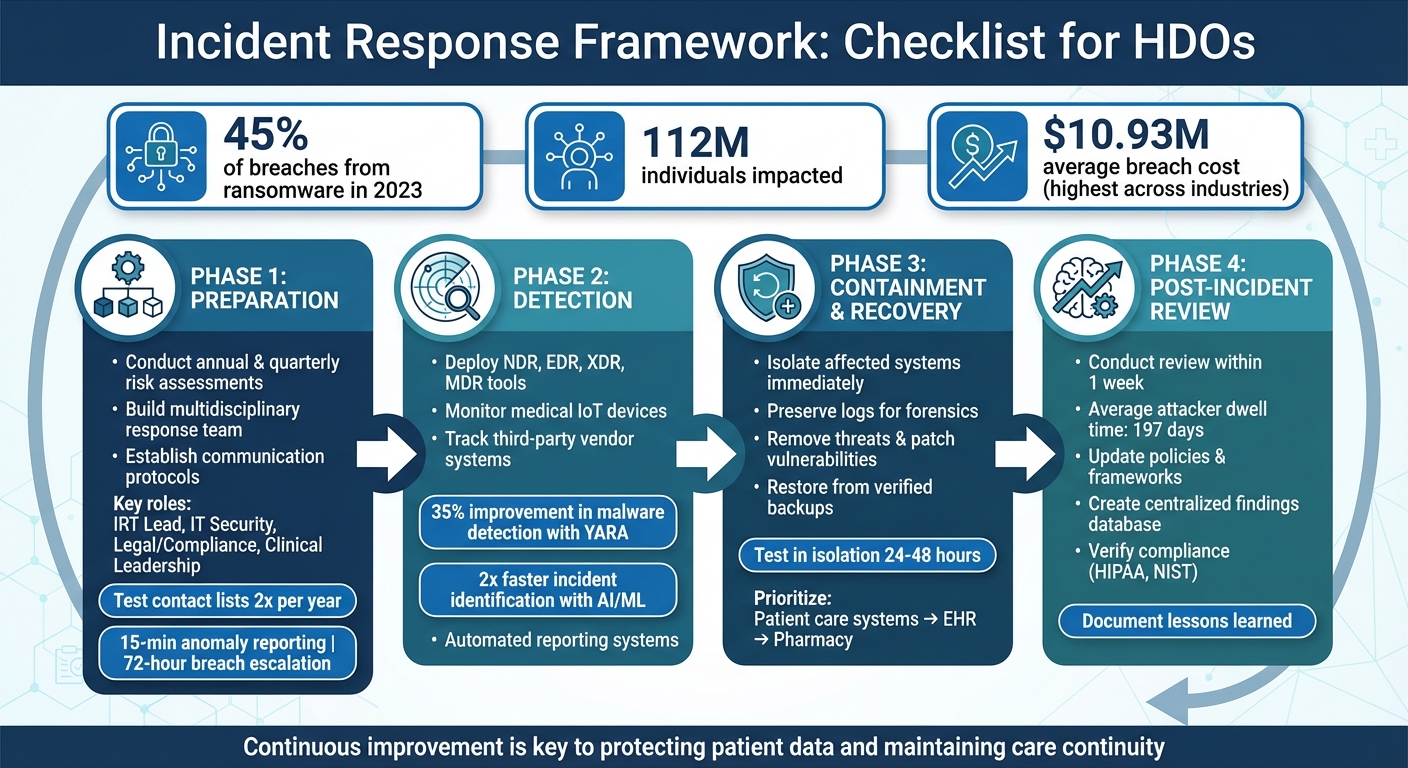
Healthcare delivery organizations (HDOs) face constant cybersecurity threats, with ransomware accounting for 45% of breaches in 2023, impacting 112 million individuals. The average cost of a breach is $10.93 million, the highest across industries. A well-structured incident response framework is critical for minimizing damage, protecting patient data, and ensuring compliance with regulations like HIPAA. Here's what you need to know:
- Preparation: Conduct annual and quarterly risk assessments, build a multidisciplinary response team, and establish clear communication protocols.
- Detection: Use tools like NDR, EDR, and MDR to identify threats early, especially in medical IoT devices and third-party systems.
- Containment & Recovery: Isolate affected systems, remove threats, and restore operations using verified backups while ensuring patient care continuity.
- Post-Incident Review: Analyze the response, update policies, and strengthen defenses to prevent future incidents.
4-Phase Incident Response Framework for Healthcare Organizations
Improving Healthcare Incident Response in the Wake of Recent Healthcare Breaches
sbb-itb-535baee
Preparation Phase: Building Your Foundation
The way your healthcare delivery organization (HDO) prepares for cybersecurity incidents determines how effectively it can respond when the unexpected happens. This phase is all about identifying weak spots, assembling the right team, and setting up clear communication systems. Without these critical steps, even the most advanced detection tools can fall short when a crisis hits.
Conducting Risk Assessments
Risk assessments are the cornerstone of incident response preparation. HDOs should conduct these assessments annually, with additional quarterly reviews for high-risk areas like medical devices and vendor systems. Major changes - such as IT infrastructure upgrades, new vendor partnerships, or system updates - call for ad hoc assessments as well.
Focus on three key areas of vulnerability: protected health information (PHI) storage and transmission, medical device networks, and third-party vendor systems. Use an all-hazards approach to evaluate not just cybersecurity risks but also broader concerns like hospital infrastructure, supply chains, and business associate agreements. Tools like Censinet RiskOps™ can simplify this process by automating third-party risk assessments and benchmarking cybersecurity performance across patient data, medical devices, and supply chain systems.
Once risks are mapped out, the next step is building a team that can act quickly and effectively when needed.
Assembling the Incident Response Team
A strong Incident Response Team (IRT) requires input from multiple disciplines to address clinical, legal, and technical challenges. Key roles include:
- Incident Response Team Lead: Oversees and coordinates the response.
- IT Security Experts: Handle technical detection and containment.
- Legal and Compliance Officers: Manage HIPAA breach reporting and regulatory compliance.
- Clinical Leadership: Focus on maintaining patient safety.
The Federal Select Agent Program also suggests adding roles like a Biosafety Officer, Occupational Health Provider, Facility Manager, and a police liaison to ensure the team covers all bases.
To keep things running smoothly, designate backups for each role and create job action sheets detailing qualifications, responsibilities, and resources. Training the team in the Incident Command System (ICS) ensures seamless integration with hospital emergency management protocols.
Once your team is ready, clear and efficient communication becomes the next priority.
Establishing Communication Protocols
Effective communication is critical to avoid confusion and delays during an incident. Set up tiered escalation protocols: anomalies should be reported to the team lead within 15 minutes, and confirmed breaches should reach senior leadership within 72 hours. Maintain a secure, up-to-date contact list that includes 24/7 numbers for team members, legal counsel, and key contacts like the HHS Office for Civil Rights (1-855-767-5224) and state health departments.
Test these contact lists and escalation procedures twice a year. Prepare pre-drafted templates for stakeholder notifications, patient safety updates, and media statements to ensure they align with HIPAA’s breach notification rules. Integrate these protocols with your Hospital Incident Command System (HICS) to ensure smooth coordination. Additionally, require that all public or media communications be approved by the incident commander before release.
Identification Phase: Detecting and Reporting Incidents
Spotting threats early is key to stopping breaches before they disrupt patient care. Healthcare organizations face an ever-changing landscape of risks, from vulnerabilities in medical devices to threats in third-party systems. The aim is to catch these issues early using a mix of automated tools and clear reporting systems.
Incident Detection Mechanisms
Effective monitoring requires multiple layers of defense across all access points. Network Detection and Response (NDR) tools play a crucial role by providing detailed insights into healthcare IT systems. These tools help protect sensitive patient information (PHI) and detect early warning signs of ransomware. According to Corelight, NDR combined with AI and machine learning can identify unusual patterns, such as scanning activities or brute-force attempts, that traditional defenses might overlook. This approach can double the speed of identifying and managing incidents [3].
For endpoints, Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) platforms ensure continuous monitoring across devices. If your healthcare organization lacks an in-house Security Operations Center, Managed Detection and Response (MDR) services can provide round-the-clock monitoring and expert threat hunting. Tools like YARA file analysis can improve malware detection rates by 35% [3].
Monitoring medical IoT (MIoT) devices and operational technology (OT) is equally important. Smart medical devices, hybrid cloud systems, and industrial control setups often introduce complex vulnerabilities. To reduce risks, focus on securing VPNs and monitoring remote vendor connections [3]. Behavioral baselining is becoming increasingly important too. While sophisticated actors, such as advanced persistent threat (APT) groups, can bypass traditional EDR tools, NDR systems are better equipped to detect subtle anomalies in network behavior [3].
Reporting and Escalation Processes
Automated reporting systems are essential for avoiding delays and ensuring compliance with CMS and HIPAA requirements. A 2023 national study revealed that only 15 out of 45 states had a single, unified incident management system for healthcare waivers, exposing the inefficiencies of outdated, paper-based processes [4].
Automated playbooks for containment - such as isolating infected endpoints or securing compromised accounts - can significantly reduce response times [5]. Regular compromise assessments are also critical for uncovering hidden threats, misconfigurations, or vulnerabilities before they evolve into major incidents [5]. Detection tools that integrate automated reporting, swift containment, and forensic capabilities make it easier to reconstruct attack timelines and identify root causes [3][5].
Using a healthcare-specific cybersecurity platform like Censinet can simplify the process further. These platforms combine detection, risk management, and response into a single solution, making incident reporting and escalation more seamless.
Containment, Eradication, and Recovery: Minimizing Damage and Restoring Services
After detecting and reporting a threat, the next step is acting quickly to contain the damage, eliminate the threat, and safely restore operations. These efforts are vital to protect patient data and ensure healthcare systems can continue functioning without compromising sensitive information.
Containing the Incident
The first priority is to isolate the affected systems to stop the threat from spreading across the network. Disconnect compromised endpoints immediately, but make sure to preserve logs for forensic analysis. Notify your incident response team and document every action taken. For physical incidents, follow established HICS (Hospital Incident Command System) protocols to secure patients and staff while recording hazards and mitigation measures [1][2].
Eradicating Threats
Once contained, the focus shifts to removing the threat. Identify all compromised accounts, malware, and vulnerabilities that led to the breach. Apply necessary patches and updates to close any security gaps. For malware infections, use forensic tools to ensure the threat is fully removed before reconnecting systems. Check all affected devices and confirm that backdoors or persistence mechanisms have been eliminated. Don’t overlook third-party vendor connections or medical IoT devices - evaluate these thoroughly and address any vulnerabilities they may have introduced.
Restoring Critical Operations
When it’s time to bring systems back online, start with verified backups. Restore these in isolation, test them rigorously, and monitor for any signs of re-infection over the next 24–48 hours. Focus first on essential services like patient care systems, electronic health records, and pharmacy operations, following your Incident Action Plan. Keep all stakeholders - clinical staff, patients, and regulatory bodies - informed about restoration timelines. Reschedule non-urgent procedures, manage staff and equipment availability, and coordinate the return of patients moved to alternate care sites during the incident [1][2]. Assign team members to oversee recovery efforts and update the Incident Action Plan as systems stabilize. These steps not only complete the response process but also prepare the organization for a thorough post-incident review.
Using advanced tools like Censinet RiskOps™ can simplify recovery by centralizing incident response and risk management activities, helping healthcare organizations regain stability more efficiently.
Post-Incident Review: Learning and Improving
Once the immediate crisis is resolved, it’s time to focus on fortifying your defenses. A solid post-incident review turns a challenging event into a chance to strengthen your systems, refine protocols, and reduce the likelihood of future breaches. Skipping this step can leave healthcare organizations vulnerable to repeated mistakes - especially when attackers, on average, linger undetected in a network for 197 days [6]. A thoughtful review sets the stage for meaningful improvements.
Conducting After-Action Reviews
Aim to conduct your post-incident review within a week of resolving the incident - or even sooner for critical events. Gather all relevant materials, including incident reports, system logs, alerts, and communication records. Build a clear timeline that tracks the event from the initial breach to its resolution. Since network forensics often captures only 2–4 weeks of raw data [6], supplement this with additional data sources to ensure a complete understanding of the incident.
"Just like architecture reviews in the R&D world or debriefs and after-action reports in the military world, we too need a process for improvement in incident management, response, containment and remediation." - Sam Curry, CSO, Cybereason [6]
Involve a diverse group of stakeholders, such as incident responders, system administrators, and clinical and technical experts, to gain a well-rounded perspective. Keep the focus on improving processes rather than assigning blame - this fosters transparency and encourages honest feedback. Have a technical lead recreate the attack chain to identify specific vulnerabilities in system configurations or network operations. Dig into the root causes instead of just addressing surface-level symptoms, and assign actionable tasks with clear deadlines to the appropriate team members.
Updating Policies and Frameworks
Use the insights from your review to update your incident response plan, refine alert thresholds, and improve communication protocols. Adjust detection mechanisms and escalation procedures based on what worked and what didn’t. To streamline future responses, create a centralized database of review findings to identify recurring vulnerabilities or attack patterns. Additionally, use current intelligence to retrospectively scan historical data for signs of backdoors or threats that may have gone unnoticed earlier in the attack.
Tools like Censinet RiskOps™ can simplify this process by centralizing updates, tracking policy changes, and managing ongoing risk assessments. This ensures lessons learned are effectively implemented across the organization.
Ensuring Compliance and Benchmarking
Assess how well your response aligned with regulatory requirements and industry standards. Review whether all necessary notifications - to government agencies, management, and affected parties - were made promptly. Evaluate the effectiveness of media relations and public communications during the incident. Verify that contact lists were up-to-date and communication channels worked as expected. Automated workflows can help maintain compliance documentation and measure your performance against frameworks like NIST or HIPAA. These steps not only ensure regulatory compliance but also strengthen your security posture, making you better prepared for future incidents.
Conclusion
Managing incidents effectively demands preparation, quick action, and a commitment to learning from every situation. Healthcare delivery organizations (HDOs) face unique challenges, needing to protect patient health information (PHI) while maintaining uninterrupted clinical services. This checklist helps organizations detect threats early, limit damage swiftly, and restore operations - all without compromising patient care. It covers key phases: preparation, detection, containment, and post-incident review, tailored to the specific needs of HDOs.
A strong incident response starts with preparation. This includes conducting detailed risk assessments, organizing multidisciplinary teams, and setting up clear communication protocols. These steps help reduce response times and limit the impact of incidents. Frameworks from WHO, CMS, and HHS also highlight the importance of post-incident reviews and compliance checks to address vulnerabilities and prevent future risks.
The post-incident review phase is where setbacks turn into learning opportunities. By documenting successes, identifying gaps, and updating policies based on lessons learned, organizations can strengthen their defenses. Continuous improvement is key to staying ahead of threats and meeting regulatory standards. These insights also emphasize the value of unified tools and streamlined processes.
Censinet RiskOps™ supports this effort by centralizing risk assessments, automating compliance workflows, and tracking policy updates. The platform helps HDOs manage third-party risks, evaluate cybersecurity performance, and maintain a cohesive incident response strategy - all while prioritizing patient safety. With the right tools and a structured approach, organizations can build resilient systems that safeguard both operations and patient care.
FAQs
What incident response metrics should an HDO track?
Healthcare delivery organizations (HDOs) need to keep an eye on several crucial metrics to maintain security and efficiency. Two key ones are incident response time - how quickly an incident is detected, addressed, and mitigated - and mean time to recovery (MTTR), which measures how long it takes to restore normal operations after an issue.
Other important metrics include impact measurements, such as the effects on patient safety and operational disruptions, as well as compliance audit scores, vendor risk ratings, and staff training completion rates. Tracking these not only highlights potential vulnerabilities but also helps streamline processes and ensures adherence to regulations like HIPAA.
How do we test backups and restore EHR safely after ransomware?
To ensure the safety and reliability of backups and the ability to restore EHR systems after a ransomware attack, HDOs must routinely check the integrity of their backups and recovery procedures. This involves creating structured testing plans, conducting simulated recovery drills, and making sure backups are secure, regularly updated, and stored across multiple locations. These steps help guarantee that backups work as intended and meet compliance standards, reducing downtime and the risk of data loss during an incident.
How should medical IoT and vendors be included in incident response?
To effectively include medical IoT devices and vendors in your incident response strategy, start by keeping a detailed and current inventory of all devices and their associated vendors. Regularly assess these devices for vulnerabilities and ensure they are fully integrated into your response plan.
It's also crucial to evaluate the incident response capabilities of each vendor. This helps you understand their role during a crisis and ensures they can assist in isolating affected devices, containing threats, and following proper reporting protocols. Routine monitoring of device health is equally important to catch potential issues early.
During incidents, work closely with vendors to address the situation promptly. This collaboration can include isolating compromised devices and ensuring compliance with regulatory guidelines. Additionally, involve vendors in testing and training exercises to ensure everyone is prepared for swift and effective responses when needed.


